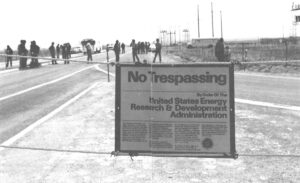
DENVER–From a distance, the high chain-link fence surrounding the Rocky Flats Plant looked like the perimeter of any other large, Security-conscious factory. Ten feet inside the main entrance, in a small cinderblock building at the side of the road, sat several uniform guards. For the most part, their duties on this March morning consisted of processing the few visitors who had official business at the government owned nuclear plant.
About mid-morning, they opened the remotely-operated industrial gate to admit a technician who had been hired by a subcontractor to inspect a construction project. As the technician’s truck passed the guard post and turned toward the project, yellow lights on the roof of the building and the gate began to flash. A loud warbling horn pierced the silence, even scaring the guards.
Immediately, the heavy gate was slammed shut, blocking the exit road. The alarm was instantly relayed to a central command post hidden away in the most secure part of the complex. From there, armed reinforcements were dispatched to track down the suspicious truck and its driver, who had inadvertently triggered a highly sensitive radiation monitor mounted alongside the roadway. The sophisticated device, which is capable of detecting minuscule quantities of nuclear material, had been installed a month earlier to guard against possible thefts from the plant. This was the first time it had signalled an actual alarm.
Moments later the guards examined the truck with even more sensitive, hand-held radiation detectors. They iminediately found the cause of the problem, a small, scaled, slightly radioactive “source.” The metallic cylinder, about the size of a pencil stub, was a standard piece of inspection equipment used to measure soil compaction. No nuclear material was being stolen or diverted. The innocent technician had merely stumbled into one of the newest devices used in safeguarding the facilities that manufacture the country’s nuclear weapons.
It’s A Whole New Ballgame
When nuclear weapons were in their infancy, the responsibility for protecting the raw materials and assembled bombs fell largely to the military police, whose techniques were derived primarily from law enforcement. As the nuclear industry grew, the approaches to safeguarding “special nuclear material,” (jargon for bombs and the weapons-grade plutonium or uranium from which bombs could be fashioned) changed dramatically. Space-age developments in computers and electronic instruments radically altered the nature of the security business.
Now the field is a high-technology horse race that relies more on the techniques of satellite spying than those of police science. Gadgets with strange names like seismic sensors, jiggle detectors, portal monitors and passive distress alarms seem to have materialized out of the latest James Bond film.
For example, delicate seismic sensors buried outside the perimeter of a weapons plant can detect the approaching footsteps of potential intruders. The devices are an extreme refinement of the technology used to warn of enemy troop movements in the jungles of Vietnam. In the most advanced systems, instant computer analysis of the electronic signals from the sensors can distinguish humans from vehicles and even estimate the number of people prowling around.
Jiggle detectors, attached to a fence, can measure the vibration caused by contact. In the best systems, the computers can distinguish vibrations caused by animals and can compensate for weather conditions such as strong gusts of wind.
Portal monitors, similar to airport metal detectors, are used at the exits from areas where plutonium and uranium are handled. Unlike the erratic airport security devices, these finely-tuned monitors will be triggered by quantities of nuclear material as small as one-thousandth of the amount required to fabricate a bomb. (In other words, a diverter would have to escape detection by the monitor a thousand times before accumulating enough plutonium for a weapon.)

Passive distress alarms worn by guards can keep track of vital signs for any sudden change. Even if a guard is seized by attackers or killed before he has a chance to sound an alarm, abrupt changes in his blood pressure and pulse rate will signal the emergency to a central command post.
With the exception of portal monitors, not all these devices are fully deployed at the seven factories and three laboratories that comprise the nuclear weapons complex. The roadway monitor at Rocky Flats was the first to be installed. However, all of the devices have been demonstrated in the labs and are in use somewhere in some form. The U.S. government has adopted a policy of ” graded safeguards,” the idea that nuclear materials with the greatest destructive potential be accorded the highest degree of protection. Plants with nearly complete nuclear weapons or large quantities of weapons-grade plutonium and uranium therefore get top priority for the newest security devices. The safeguards system around the country is constantly in a state of transformation and security officials are understandably reluctant to boast of their most sensitive equipment or admit weaknesses due to older, less refined gear. Within the next few years, much more of the advanced hardware will be deployed at the weapons plants.
The Start of a Building Boom
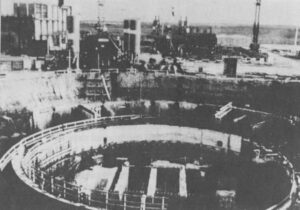
The U.S. Department of Energy has already spent $5 million on a “perimeter intrusion detection and assessment system” incorporating many of these devices at its Pantex Plant near Amarillo, Texas. The facility, a munitions factory during World War 11, has been used since 1951 for the final assembly of nuclear weapons. Because it is the only unit in the production complex handling finished weapons, DOE provides Pantex with the highest level of protection.
Another $5-million project for an advanced “perimeter security zone” is underway at Rocky Flats. Next year, DOE will complete a $3-million “long-range alarm system” at the Los Alamos National Scientific Laboratory in New Mexico. Improved security systems also have been installed at the Oak Ridge National Laboratory in Tennessee and Portsmouth uranium-enrichment plant in Ohio. Other plants in the complex also will be getting major security improvements in the next few years as a small part of a much larger program to renovate the entire nationwide weapons-production apparatus.
In all, the government will be spending about $2.3 billion by 1986 to modernize and expand its facilities for producing nuclear weapons.
This building boom was launched quietly by President Jimmy Carter in 1979 in anticipation of sharply higher production rates for nuclear weapons during the 1980s. Carter’s military advisors pointed out that much of the U.S. stockpile, manufactured in the early 1960s, would be getting unreliable after twenty years of radioactive decay. Technological improvements in electronic detonation components and safety features were already making much of the arsenal obsolete. During the 1980s, major new weapons systems would be ready for deployment-the Trident submarines, cruise missiles, and possibly the MX and the enhanced-radiation weapons (the so-called “neutron bomb”). Other systems like the aging Minuteman III missiles would have to be overhauled. The basic strategic nuclear bomb used by the Air Force in its B-52s for more than twenty years would be ready for replacement by a weapon of improved design.
All this activity would be coming at a time when the weapons plants, which were built in the 1940s and 1950s, would be wearing out. Weapons production had fallen during the 1970s as the plants were overtaken by the effects of old age. For years, the Assistant Secretary of Energy for Defense Programs had been pushing the congressional appropriations committees for more money to rebuild the deteriorating plants. Each year, the lawmakers saw another closed-door slide show of corroded pipes, broken generators, antiquated machine tools and overcrowded assembly lines. Before the weapons complex could boost production 50 or 100 percent to keep up with the foreseeable workload, it had to be rebuilt.
The sharply higher production rates would also mean thousands of new employees in the weapons plants and tons of additional nuclear materials. That, in turn, would require an overhaul of the safeguards and security systems, particularly in light of the enormous improvements in the technology of the field.
Before a safeguards system can be designed, planners must decide what kind of threat the system must be able to foil. Everything begins with the formulation of “an accurate, comprehensive profile of the attributes and intentions of these adversaries,” George Weisz explained to a congressional committee in 1979.
Weisz, 63, is a short stocky man who speaks with a slight British accent. Born in Hungary, he emigrated to the United States in the 1930’s, then spent 30 years working on unspecified “national security matters” for the Departments of State and Defense. Two and a half years ago he moved over to DOE to become director of the Office of Safeguards and Security -the man in charge of protecting DOE’s weapons and special nuclear materials.
Weisz explained that most of the $50-million budget required to run his office goes into research and development, perfecting the sophisticated detection devices and computer systems. A large portion is spent to coordinate and evaluate the security measures of the private contractors who operate the weapons plants for DOE. Altogether, those contractors- such companies as Rockwell, DuPont, Monsanto, Bendix, GE and Union Carbide-spend another $175 million on safeguards for their plants.
Analog Studies
Basic to safeguarding is the process of “threat characterization.” Since there has never been a hostile attack on a U.S. nuclear weapons plant, the planners have no direct experience on which to base their estimates. Some information about possible threats comes from the FBI and the CIA, but most of it comes from think-tanks like the Rand Corporation, which routinely examines serious crimes around the world that may hold a message for U.S. weapons plants. These “analog studies” show the size, motivation, skill and resources of typical criminal groups. In the early 1970s, the most likely threat was considered to be a small band of outsiders, maybe three people, armed with automatic weapons, probably operating with insider assistance.
After the attack by Palestinian terrorists at the Olympic Games in Munich in 1972, the nature of the threat was revised. The group might be larger, perhaps as many as 15 or 20 people. They would be well financed and trained, heavily armed and highly dedicated, probably even fanatical. And they too would have assistance from one or two insiders.

Weisz’s 34-year-old deputy director, Tom Issacs, noted in a recent interview that there now is “almost no limit” to the resources that a terrorist group could bring to bear. The boldness and ingenuity of terrorist operations clearly showed a dramatic expansion of the limits. Who could have anticipated the kidnapping of eleven OPEC oil ministers by the infamous “Carlos the Jackal” in Vienna in 1975, the abduction and murder of Italian premier Aldo Moro by the Red Brigades in Rome in 1978, or the occupation of Islam’s most holy shrine, the mosque at Mecca in 1980?
Tom Issacs is typical of the new breed of safeguard specialists. Formerly a chemical engineer with the Atomic Energy Commission, he completed graduate work in science and public policy at Harvard and MIT. Threat assessment is the “considered judgement of reasonable people, ” he explained. “There’s no defined methodology because it’s partly an art. “
The Office of Safeguards and Security is about to issue a new “threat guidance paper” containing subtle changes. Terrorists will remain as the primary focus, but there will be additional emphasis on the possibility of theft or sabotage by insiders-disgruntled employees or the lone psychopathic individual described by Rand analysts as the “flaming banana.” The new assessment has its origins in two troubling incidents at plants licensed by the Nuclear Regulatory Commission:
In January, 1979, employees at a General Electric plant in Wilmington, North Carolina, discovered that two canisters of slightly-enriched uranium used in the manufacture of fuel rods for commercial reactors were missing. An extortion note demanded $200,000; otherwise the 140 pounds of brown, sandy uranium oxide would be sent to public figures or dumped in a busy intersection of a large city. The material was essentially harmless and could not be used in the fabrication of a nuclear weapon; the only danger was psychological. Within a week the FBI arrested a temporary employee of a GE contractor who had access to the plant. (He was convicted of extortion and imprisoned.)
In May 1979, officials at the Surry nuclear power plant near Williamsburg, Virginia, were shocked when they found that 62 unused fuel assemblies stored in a supposedly secure area had been deliberately damaged. Someone had poured a caustic substance on the valuable fuel rods owned by the Virginia Electric Power Company. A month later, two employees training to be reactor operators held a press conference and explained that they had done the damage to dramatize alleged safety problems at the Surry plant. (The NRC refuted most of their claims in the subsequent investigation. The two were convicted on state charges for the destruction of private property and are now in prison.)
To safeguard analysts these incidents marked the emergence of a new phenomenon in the nuclear industry-malevolent acts by insiders. Research since then has focused more heavily on potential problems from people inside the system.
While these studies were still in progress, DOE officials were given something else to think about. Last fall, the FBI discovered that 200 employees at the Sandia Laboratories in Albuquerque were using a government computer for such personal business as keeping track of a loan-repayment schedule and cataloging a beer-can collection. One programmer was using it to develop an accounting system for bookies. The incident wasn’t as serious as the two occurrences of sabotage because no malevolence was involved at Sandia, just the normal exuberant creativity of computer enthusiasts. Nevertheless, the unusual use of the computer illustrated an absence of internal controls and a vulnerability to potential sabotage. These revelations were especially embarrassing because the lab, operated by Western Electric Company, is part of DOE’s weapons complex and conducts most of the research on security hardware and procedures.
Defense in Depth
The key elements in the safeguarding of nuclear materials are common knowledge: access control, multiple barriers, accounting measures, reliable communications, and rapid response forces.
The system begins with background checks, usually by the FBI, when an employee is hired. Access to nuclear materials is restricted to people with proper security clearance. This procedure is far from foolproof, however. The growing legal protections assuring the right of privacy, officials complain, make the job of background checks much tougher. Clever imposters and unreliable applicants occasionally slip through. The process may tend to discourage bad apples from applying rather than expose them, Issacs explained.
Therefore, the first line of defense remains physical protection and that’s where most of the space-age hardware comes into play. The goal is to assure immediate detection of a threat and a quick reaction. In theory, before potential intruders could breach the outer fences, guards would be shooting at them. By then, reinforcements from local police agencies, military units and the FBI would already be on the way.
The plan envisions that the attackers would be successful at first, but that they would then encounter a series of obstacles -“defense in depth”- and would have to fight while overcoming each of them. Issacs noted that the adversaries would have to work their way through a “maze” and make the proper moves at every juncture.
The barriers are designed to be diverse. A wide range of skills, from knowledge of electronics and explosives to mastery of computers, would be required to defeat them. This diversity places a premium on the training and resources of the attackers and increases the probability of failure when one of the intruders is killed. The hostile force would have to fight its way out of the plant as well as in.
Though Issacs was speaking of the nuclear weapons plants under the control of DOE, the same general principles apply to the safeguarding of nuclear power plants as well. The government agencies try to adhere to the doctrine of “comparability” -that nuclear materials of comparable attractiveness for theft or diversion will be accorded comparable levels of protection regardless of the agency with jurisdiction. Periodically, representatives of DOE, the Nuclear Regulatory Commission, and the Department of Defense meet to discuss common standards. The safeguards applied by all three, therefore, are similar.
Because nuclear power plants do not contain material as readily converted to bombs as the weaponsgrade material handled by DOE facilities, they are not as strongly defended. Still, much of the esoteric hardware first deployed at the weapons plants is now being installed at nuclear power plants.
An Unsolvable Problem
Countering the insider threat is a more subtle discipline-a chess match that is less likely to end in a shoot-out. The security hardware like portal monitors is a substantial deterrent, but the best defenses are built into design and accounting. Increasingly, the production activities in the weapons plants are being automated and controlled remotely. It is an important side effect of a plant design which isolates employees from nuclear material that it also reduces opportunities for theft or diversion.
The most effective countermeasure, however, is a fast, accurate sensitive system of measurement and accounting that can detect very small thefts as they occur. Such highly computerized systems are already used in some of the weapons plants and are under development in others. The first such system was installed at the plutonium-fabrication facility at the Los Alamos National Laboratory in 1978. (A relatively unsophisticated computer tracking system uncovered the theft from GE’s Wilmington plant hours before the extortion note arrived.)
Despite all the research that has gone into safeguards, the analysts are still at a primitive stage in measuring the effectiveness of their creation and the risk to the public. At the moment, they evaluate the safeguards system by testing procedures in paperwork exercises, computer simulations, and actual attempts at penetration. In these “black-hat” games, the bad guys devise a plausible scenario based on a perceived weakness in the system, then walk through their plans until they succeed or are frustrated. The system is then modified in response to the outcome.
This procedure closes loopholes, but it does not provide a means of describing how much protection the government is buying with all its expenditures. “We’re kidding ourselves if we think the risk can be quantified,” Tom Issacs said.
There are no absolute or static answers to the nature of the threat to nuclear material and to society. The threat and the possible responses are always changing. The chances of success or failure of the safeguards system, and the resulting effects on the public, depend on the deliberate human actions of the safeguards and their adversaries-on their willful intent.
“It’s not a problem that can be solved,” Issacs said. “It’s an ongoing concern.”
©1981 Ron Wolf
Ron Wolf former editor of Straight Creek Journal, lives in Denver, Colorado. He is investigating the safeguarding of nuclear materials in the U.S.